Mobile apps form one of the mainstays of today’s business world. From streamlining communication and collaboration to increasing productivity and efficiency, these applications offer numerous benefits. However, along with the benefits, there are also inherent risks.
The increased reliance on mobile apps in corporate environments, combined with, in some cases, lax cybersecurity practices among employees, has made mobile apps a target for threat actors. According to Verizon, 45% of organizations experienced a breach related to mobile devices last year. Another study found that more than half of employees admit to using unauthorized apps for work purposes.
Although these statistics present a harsh reality, there are some strategies that can help businesses survive unscathed. Here are seven steps to balance security with a seamless mobile experience in your enterprise environment.
Step 1: Scrutinize the app.
Organizations need to take an insightful approach to app selection. This requires a deep dive into the application’s security protocols, functionality, and data privacy practices. We examine app permissions, encryption standards, data retention policies, and developer reputation. Prioritize trusted marketplaces where apps undergo rigorous reviews and malware scans, such as the Google Play Store and Apple App Store. The company minimizes the risk of malicious or unauthorized software entering its network by restricting app installations to a carefully curated whitelist.
Step 2: Encrypt your data.
We implement industry standard encryption to protect all data stored on your mobile device and transmitted through the app. This protects sensitive information even if your device is lost or compromised. Encrypting data in transit has become a powerful technique for thwarting man-in-the-middle (MITM) and traffic sniffing attacks that can severely impact corporate networks. To prevent such exploits, use a reputable VPN service.
Step 3: Manage your devices using MDM.
Mobile devices used for organizational purposes require attention, especially in an era where digital governance is becoming increasingly prevalent. Mobile device management (MDM) products allow businesses to enforce security policies, monitor device usage patterns, and remotely wipe data if a device is lost or stolen. MDM policies should go beyond the basics and encompass elements such as encryption, multi-factor authentication, and a commitment to timely security updates.
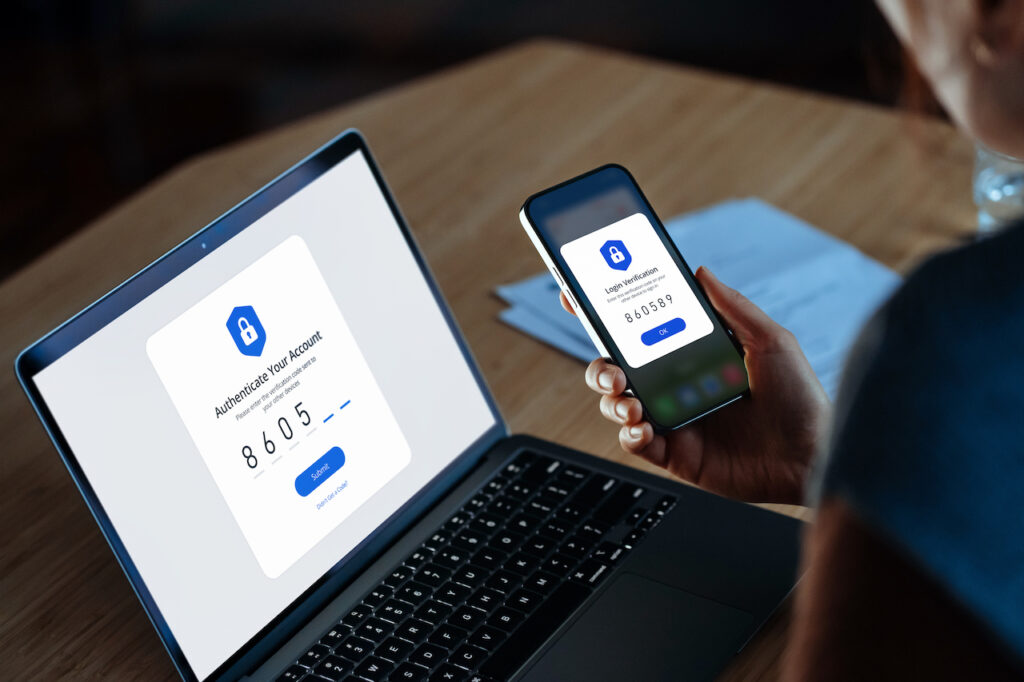
Step 4: Verify with MFA and DLP.
An impactful cyberattack can start with a single compromised account. This was reportedly the case with the massive breach of leading Ukrainian mobile operator Kyivstar that occurred in December last year and caused mobile connections to go down for several days in around half of the country. That’s what it means. This recent incident confirmed the importance of proper employee authentication.
Password management and multi-factor authentication serve as additional layers of defense against such abuse. Data loss prevention (DLP) systems can take this a step further. Prevent unauthorized data sharing and downloads and keep sensitive information within designated channels.
Step 5: App developers and corporate IT collaborate.
The responsibility for mobile application security does not rest solely with the end user. That extends to the developers who create these programs. A collaborative effort between a company’s IT team and app creators is essential to ensure DevSecOps is a reality. For example, if an organization is considering implementing a company-wide QR code generator, it is recommended to ensure that the product is GDPR and SOC 2 compliant and to discuss this with the developer beforehand. To do. Also include regular updates and patches on your checklist. The symbiotic relationship between businesses and app makers helps build robust defenses against evolving cyber threats.
Step 6: Develop and communicate your incident response plan.
When a security breach occurs, a clearly defined incident response plan is the key stepping stone to recovery. Quick and coordinated actions can help reduce the impact of attacks and prevent further breaches. Establish clear communication channels and protocols for reporting suspicious activity related to mobile applications. This ensures that the response is not only timely, but also well-informed.
Step 7: Educate your staff on how to identify security holes.
Technology alone is not enough. The human element remains a prominent factor in security breaches, making it critical to train employees on responsible app usage, phishing awareness, and how to report suspicious activity.
By prioritizing security and taking proactive steps to reduce risk, businesses can leverage the full potential of mobile apps to meet KPIs without exposing data to malicious actors. Complete important tasks on the go. Enterprise security requires a holistic approach, making securing the mobile ecosystem a key component of this strategy.
David Balaban, Privacy-PC Owner