Microsoft announced Thursday that it will once again disable the ms-appinstaller protocol handler by default after multiple threat actors exploited it to distribute malware.
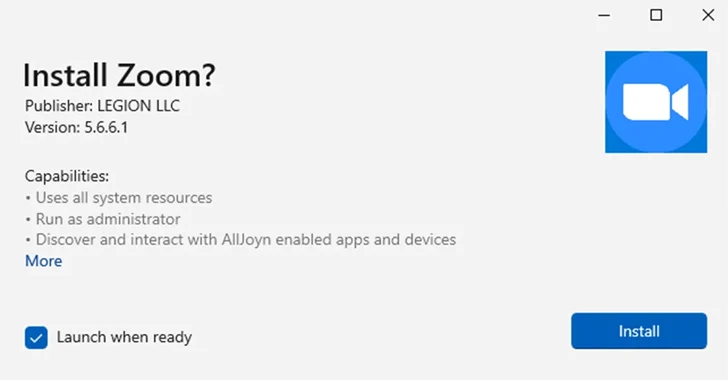
The Microsoft Threat Intelligence team stated that “observed threat actor activity is exploiting the current implementation of the ms-appinstaller protocol handler as an access vector for malware that could lead to the distribution of ransomware.” Ta.
Additionally, we noted that several cybercriminals are selling malware kits as a service that utilize the MSIX file format and the ms-appinstaller protocol handler. This change took effect in App Installer version 1.21.3421.0 and later.
This attack takes the form of signed malicious MSIX application packages distributed via Microsoft Teams, or malicious advertisements for legitimate popular software on search engines such as Google.
From User to Administrator: Learn how hackers gain full control
Discover the secret tactics hackers use to gain control and how to detect and block them before it’s too late. Register for the webinar now.
Join now
Since mid-November 2023, at least four financially motivated hacker groups have been observed leveraging app installer services and using them as entry points for subsequent ransomware campaigns.
- Arashi-0569propagates BATLOADER through Search Engine Optimization (SEO) poisoning by sites impersonating Zoom, Tableau, TeamViewer, and AnyDesk, uses malware to deliver Cobalt Strike, and storm-gathers access for Black Basta ransomware deployment. Early access broker to hand over to 0506.
- Arashi-1113an early access broker that distributes EugenLoader (also known as FakeBat) using a fake MSIX installer disguised as Zoom, and acts as a conduit for various stealer malware and remote access Trojans.
- sangria tempest (also known as Carbon Spider and FIN7). Uses Storm-1113’s EugenLoader to drop his Carbanak, delivering an implant called Gracewire. Alternatively, the group used Google ads to trick users into downloading a malicious MSIX application package from a fraudulent landing page and distributed POWERTRASH, which was used to load NetSupport RAT and Gracewire.
- Arashi-1674uses the TeamsPhisher tool to send a fake landing page disguised as Microsoft OneDrive or SharePoint through Teams Messages, prompting recipients to open a PDF file that, when clicked, updates Adobe Acrobat Reader and launches a malicious page. An early access broker that prompts you to download an MSIX installer. Contains a SectopRAT or DarkGate payload.
Microsoft also used Storm-1113 “as-a-service,” providing malicious installers and landing page frameworks that mimic well-known software to other threat actors such as Sangria Tempest and Storm-1674. I explained that it is an entity that does

In October 2023, Elastic Security Labs details another campaign that used fake MSIX Windows app package files for Google Chrome, Microsoft Edge, Brave, Grammarly, and Cisco Webex to distribute a malware loader called GHOSTPULSE. Did.
This is not the first time Microsoft has disabled the MSIX ms-appinstaller protocol handler on Windows. In February 2022, the tech giant took the same step to prevent threat actors from weaponizing it to distribute his Emotet, TrickBot, and Bazaloader.
“Threat actors may have chosen the ms-appinstaller protocol handler vector to leverage mechanisms designed to protect users from malware, such as Microsoft Defender SmartScreen and browsers’ built-in warnings for downloading executable file formats. Microsoft says.